扩展4:业务系统的数据分析
本章节我们拓展业务系统的数据分析
todo
开启ELB访问日志
todo 目前请跳转至 http://bigdata.awspsa.com/ 查看类似步骤
使用Glue获取访问日志的表结构
使用Athena查询分析日志
使用superset制作数据分析可视化dashboard
使用Glue对接RDS postgreSQL进行ETL
RDS postgreSQL数据和ELB日志数据进行聚合查询
开启ELB访问日志
部署 Kubernetes Metrics Server
请SSH至您的堡垒机,例如:
ssh -i "odoo.pem" ec2-user@ec2-54-176-92-104.us-west-1.compute.amazonaws.com
ps:如果您已经为本地的aksk添加了configmap的授权,您也可以在本地执行后续的操作。
通过以下命令部署 Metrics Server
kubectl apply -f https://github.com/kubernetes-sigs/metrics-server/releases/download/v0.3.7/components.yaml
验证 Metrics Server 是否部署成功请执行以下命令:
kubectl get deployment metrics-server -n kube-system
输出:
NAME READY UP-TO-DATE AVAILABLE AGE
metrics-server 1/1 1 1 11s
- Kubernetes Metrics Server 是集群中资源使用情况数据的聚合器,它在 Amazon EKS 集群中默认不部署。Kubernetes Dashboard 使用 Metrics Server 来收集集群的指标,例如 CPU 和内存随时间的使用情况。
部署 Kubernetes Dashboard
通过以下命令部署 Kubernetes Dashboard
kubectl apply -f https://raw.githubusercontent.com/kubernetes/dashboard/v2.1.0/aio/deploy/recommended.yaml
输出
namespace/kubernetes-dashboard created
serviceaccount/kubernetes-dashboard created
service/kubernetes-dashboard created
secret/kubernetes-dashboard-certs created
secret/kubernetes-dashboard-csrf created
secret/kubernetes-dashboard-key-holder created
configmap/kubernetes-dashboard-settings created
role.rbac.authorization.k8s.io/kubernetes-dashboard created
clusterrole.rbac.authorization.k8s.io/kubernetes-dashboard created
rolebinding.rbac.authorization.k8s.io/kubernetes-dashboard created
clusterrolebinding.rbac.authorization.k8s.io/kubernetes-dashboard created
deployment.apps/kubernetes-dashboard created
service/dashboard-metrics-scraper created
deployment.apps/dashboard-metrics-scraper created
验证 Kubernetes Dashboard 是否部署成功请执行以下命令:
kubectl get deployment kubernetes-dashboard -n kubernetes-dashboard
输出:
NAME READY UP-TO-DATE AVAILABLE AGE
kubernetes-dashboard 1/1 1 1 14m
设置 Kubernetes Dashboard 访问代理 kube-proxy
kubectl proxy --port=8001 --address=0.0.0.0 --disable-filter=true &
打开您的游览器,请使用 Web 浏览器打开dashboard的URL,URL需要您手动进行替换,您可以替换为DNS地址或者公网IP地址,DNS就是您刚刚ssh的那段地址,IP地址您可以通过EC2的控制台查看。替换后的URL例如:
http://<替换为您的堡垒机公网DNS或IP地址>:8001/api/v1/namespaces/kubernetes-dashboard/services/https:kubernetes-dashboard:/proxy/#!/login
打开登录页面后,dashboard会要求我们输入凭证,我们需要进行如下操作获取凭证。
创建一个用于访问 Kubernetes Dashboard 的服务账号,并使用其 Bearer Token 令牌访问
- 创建服务账号,并绑定集群角色,在您的堡垒机运行以下命令
cat << EOF > dashboard-access.yaml
apiVersion: v1
kind: ServiceAccount
metadata:
name: admin-user
namespace: kubernetes-dashboard
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: admin-user
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: admin-user
namespace: kubernetes-dashboard
EOF
执行命令部署ServiceAccount,并将凭证打印到屏幕上
kubectl apply -f dashboard-access.yaml
输出
serviceaccount "eks-admin" created
clusterrolebinding.rbac.authorization.k8s.io "eks-admin" created
再执行
kubectl -n kubernetes-dashboard describe secret $(kubectl -n kubernetes-dashboard get secret | grep admin-user | awk '{print $1}')
输出
Name: eks-admin-token-b5zv4
Namespace: kube-system
Labels: <none>
Annotations: kubernetes.io/service-account.name=eks-admin
kubernetes.io/service-account.uid=bcfe66ac-39be-11e8-97e8-026dce96b6e8
Type: kubernetes.io/service-account-token
Data
====
ca.crt: 1025 bytes
namespace: 11 bytes
token: <authentication_token>
- 现在我们拿到凭证,请复制令牌(以上token的部分),并使用令牌访问 Kubernetes Dashboard
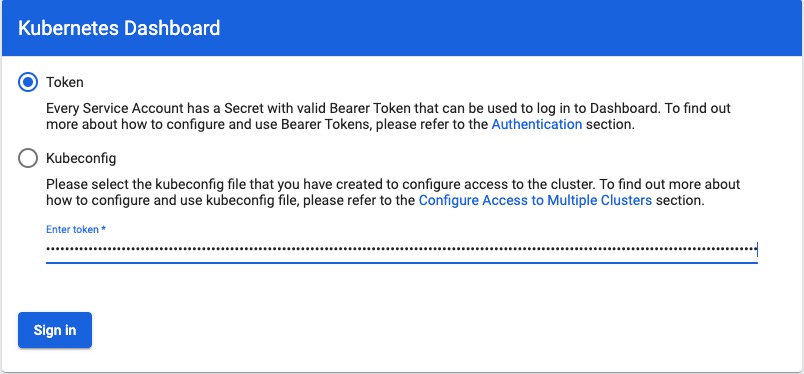
访问 Kubernetes Dashboard